

Jennifer Brown March 12, 2008
Anyone responsible for corporate risk assessment knows that keeping tabs on the threat landscape is a much weightier task than it was a decade ago. From security and safety risks to environmental and brand protection documenting risk is a process that has moved beyond the realm of just a pen and paper checklist. It’s also a concern that feeds into virtually every business unit.
“One of the foundations of security planning is that you have a form of assessment from which to draw your mitigation, so you assess to a set of rules or standards and from that you develop the mitigation plan,” says Doug Powell, manager, corporate security at B.C. Hydro.
Corporate security at B.C. Hydro is an intellectual department that handles policy, procedures, standards and guidelines, and conducts audits. “We take the mitigation strategy to the business unit that is responsible and we ask them to implement.”
Like most corporations, B.C. Hydro has developed in an ad-hoc way over the years and one of Powell’s tasks in the last year has been to create a risk assessment standard and then move towards assessing facilities and coming up with a common mitigation strategy.
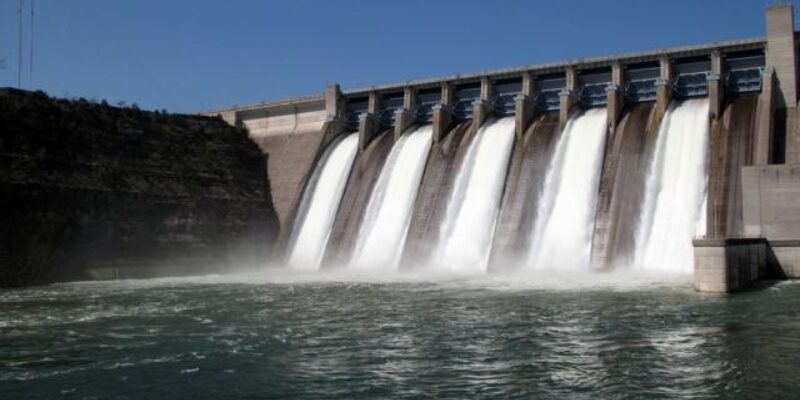
The utility operates numerous integrated hydroelectric generating stations, two gas-fired thermal power plants and one combustion turbine station. With 100 facilities located across the province, ranging from small powerhouse buildings to large dams, coming up with a tool to evaluate risk at the various sites that could scale was critical. When Powell went looking for something to measure risk for the corporation’s diverse locations, he knew the tool had to take into consideration the range of facilities. In the past, risk assessment was done with pen and paper and the process was based on the RCMP’s security assessment format. “A number of the people who were doing the security assessments for B.C. Hydro were retired RCMP officers and they were simply drawing on the forms they knew,” says Powell.
Recognizing that different individuals in the industry come with different skill sets and that B.C. Hydro still relies on a number of consultants to provide threat-risk assessments, Powell wanted to find a tool that would help standardize the threat report process, and the kind of report he would receive.
“We often got a wide variety of reporting formats — some would assess on a quasi all-hazards approach, while some would do it from a terrorist approach and others would just use pen and paper methodology, looking at security from a layered protection approach. But we wanted an all-hazards approach first, secondly to be standardized and thirdly it had to be measurable against something,” he says. “We wanted something that would provide us a common format and process no matter who was doing the assessment.”
Powell ended up choosing two products from Toronto-based FutureShield to get a better picture of the risk across B.C. Hydro. At the same time, he was also shopping for an incident management system that would allow the organization to create its own searchable fields, manage existing and future case loads and daily task requirements and meet their multiple reporting needs. Powell went with D3 Security Management Systems software and Asvaco Threat Risk Assessment software, which provided a FEMA and NFPA 1600 standard that B.C. Hydro could measure their risk against. Both of those standards are U.S-based, however, due to a lack of Canadian standard to measure against, it was the highest bar Powell could find to measure his organization against.
“We ran into two problems when we were sourcing software for this — one was that there was no Canadian software that we felt that would do the job for us that was developed in Canada that was either all-hazards in approach, or holistic enough for us to go out and do anything from a major dam to a small power house. The second is there really aren’t any standards folded into security practices in Canada. We would have had to build them in ourselves.”
There are other standards Powell can draw from, including the standards developed at B.C. Hydro corporate security, but the team would have had to develop its own software which would have taken a couple of years.“The U.S has always lead in terms of security standards — a lot developed by the military in the U.S. for protecting installations and NFPA 1600 is not security per se, but emergency management and response and now we have TSA 1600,” says Powell.
The utility will explore use of the software tool around emergency management, critical asset inventory and other related needs. An additional benefit is the software can be used across other business units for environmental assessment and some safety audits. The organization can also create a catalogue of assets, add video files and photograph files and a number of other multi-media files.
“In an emergency we can draw from those files to remind us what the facility looked like, what the weaknesses were, what the critical processes of that facility were — it becomes a tool of record that we can draw from for a number of reasons or that other disciplines within B.C. Hydro can use to assess their own area,” he says.Operating under a 60-day window after the purchase of the software, Powell conducted a pilot project in a field office in the Kootenays and did a full workup on that facility to make sure the software did what it promised.
“It’s very scalable software — once you’ve identified the threat and risk hazards and impact — when you’re actually looking at the facility you have four options to choose from: Tier 1, Tier 2, Tier 3 and Tier 4. Tier 1 is a basic assessment — a building with four walls and a couple of rooms inside; not a very important facility in terms of threat ranking.”
Tiers 2 and 3 are more significant in complexity and Tier 4 requires the evaluator to put themselves in the mind of a terrorist and create terrorist profiles of who could attack the facility and how they would do it. “It is a counter-terrorism component that allows you to do a lot more mapping,” says Powell.
Powell’s plan was to conduct risk assessments on one-third of the 100 facilities in the corporation in 2007, one-third in 2008 and the balance in 2009. “We will then have a mitigation strategy to upgrade all facilities over the next four years,” says Powell, adding a number of facilities have been identified as needing upgrades.Fortunately, the facilities department had already agreed to fund whatever mitigation strategies were agreed to.
A third of the way through the risk assessment process, Powell says the biggest benefit is having a standardized approach no matter what facility is being evaluated or how complex or how critical the infrastructure is.
“It’s a standard approach to measurement and an all-hazards approach which is really important because we are dealing with a common set of drivers that are used throughout the industry and North America.”It also gives the executive team a snapshot of not only what risk sits in the company, it pinpoints where the risk is specifically.
“When our enterprise risk management group does its monthly reporting to the executives they can map the work we are doing which also highlights that work” he says.
Return To The Press Room